They finally did it.
-
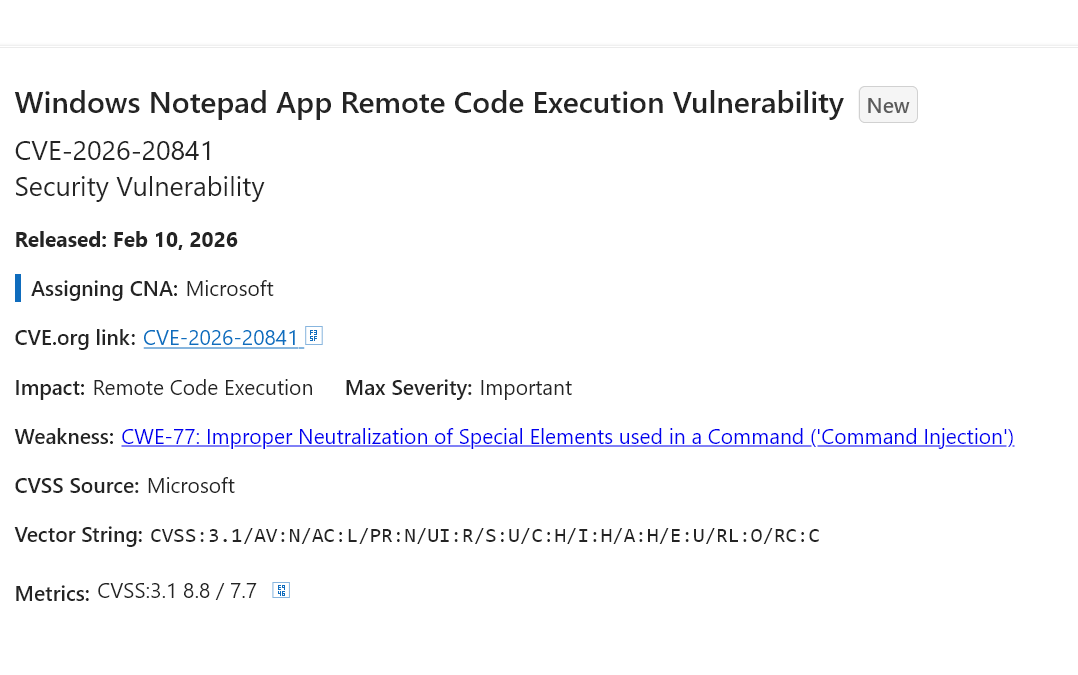
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
I'm not surprised...
A simple
cat <file>on the command line can also compromise your system. If you're unsure, you should therefore usecat -v <file>when I'm not mistaken. -
@ClickyMcTicker @pheonix There is no problem with it with the newest version 8.9.1
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix nothing can be safe. It is computing. That ship has sailed a loooooong time ago
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix *vibe-coding intensifies*
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix Idk how the fcuk they can mess up a simple notepad application. When you add junk (Copilot) it's kinda expected lol. #microslop f-ing company 🤮
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix
Notepad?? FRIGGIN NOTEPAD? HOW DO YOU SCREW UP SOMETHING LIKE A BASIC-ASS TEXT EDITOR PROGRAM? -
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix This is the most vibe slop, ever!

-
@pheonix
Notepad?? FRIGGIN NOTEPAD? HOW DO YOU SCREW UP SOMETHING LIKE A BASIC-ASS TEXT EDITOR PROGRAM? -
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix According to the report you have to click a link in the file, just loading it won't compromise the system.
-
@ClickyMcTicker @pheonix There is no problem with it with the newest version 8.9.1
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix Nothing from Microsoft, no.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix That's what you get for using AI in development. What could possibly go wrong?
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix How can you fuckup Markdown support so hard
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix
STOP UPDATING NOTEPAD(source: https://www.reddit.com/r/windowsmemes/comments/1plqsi2/stop_updating_notepad/)
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
not the first one, not the last one

CVE-2019-12735 CVE-2002-1377 CVE-2016-1248 CVE-2021-43908 CVE-2023-36742 CVE-2020-27955 CVE-2007-5795 CVE-2022-48337 CVE-2024-25255 CVE-2025-49144 (
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix MicroSlop CraPilot.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix what's an unverified protocol?
-
@pheonix According to the report you have to click a link in the file, just loading it won't compromise the system.
@jkb @pheonix That seems to be the case, although the weakness is in Microsoft Notepad incorrectly handling “an unverified protocol”, not in something the user then has to do or interact with. Besides clicking a link.
This reads to me like an URI protocol handling issue.
And that functionality is not something they’d have to reinvent or vibe code.
You know, with their proprietary plain text editor running on their proprietary OS, and next to their proprietary file explorer, their proprietary internet browser, their proprietary email client and proprietary network agents.
All their proprietary software handling URI protocols… RIGHT THERE.
-
@pheonix
Notepad?? FRIGGIN NOTEPAD? HOW DO YOU SCREW UP SOMETHING LIKE A BASIC-ASS TEXT EDITOR PROGRAM?@trillytrill I know, right? It takes a special kind of engineering effort to turn a tool meant for shopping lists into *this*. We've reached the final boss of over-engineering!


-
@pheonix *vibe-coding intensifies*
@gabrielesvelto The vibes are definitely...high-decibel today. Stay safe out there!