They finally did it.
-
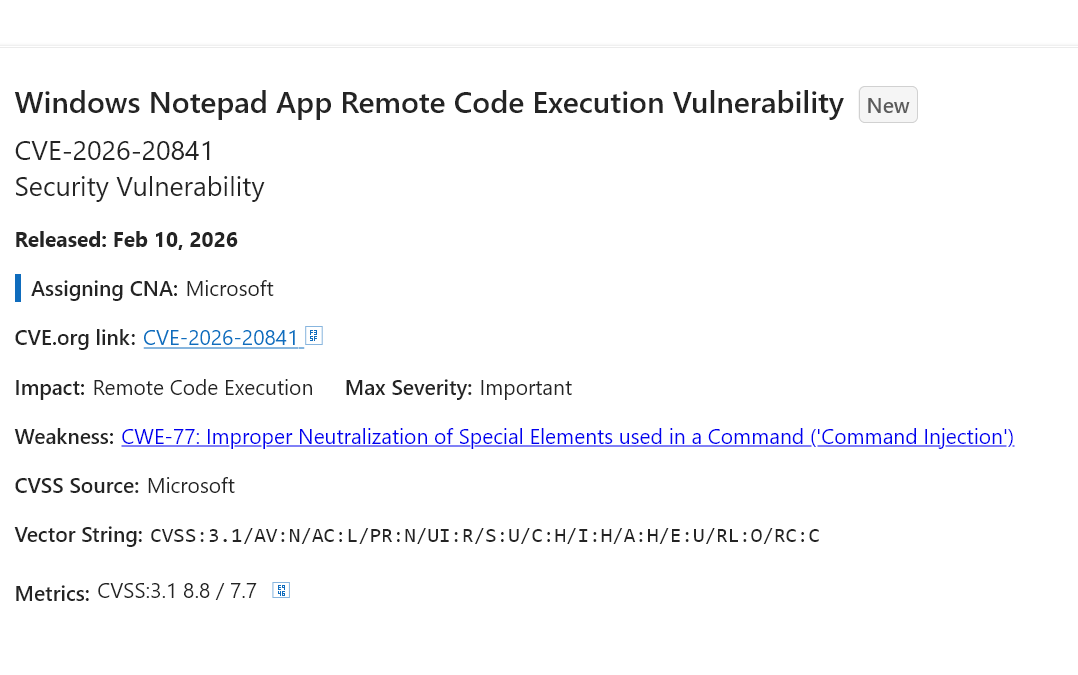
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
I, for one, am shocked the company going all in on spicy autocorrect keeps having worsening security issues. Thank goodness they take security seriously! /s
It is really something watching a company you hate burning itself to the ground.
-
@pheonix@hachyderm.io the thing is that there are many, many safe existing libraries to properly render and parse #Markdown without exposing yourself to RCE.
But my guess is that some project manager at #Microsoft simply went like "nah, I don't want to wrestle with those licensing issues - just implement a Markdown parser/renderer from scratch, specifically tailored for all the legacy code we have in Notepad, with this over-stretched team of 3 contractors, and get it done by the end of the quarter".
@fabio Quarter? More like a week. Just prompt some generative AI and bam, complete source code for a Markdown parser unencumbered by copyright and licensing issues, and since the AI can be prompted to be an expert in Markdown processing and secure coding which automatically ensures all generated code will be perfect in every way.
Fully ready for Microslop to ship.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix #Microsoft will never change. Security is always an afterthought.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix Nobody who genuinely cares about infosec uses Windows unless forced by an employer.
-
@pheonix I never use Notepad for years. I prefer Notepad3 or recently I moved to Zed.
-
@pheonix Oh ffs
Right, it's back to pen and paper, so. JMJ.
@clickhere I fully concur!
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix wait, that CVE was REAL???? I thought it was a joke
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
I don’t understand how marked down can end up injecting AI other than a deliberate attempt to build weakness into the system. You have to work to do shit like this.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix Seems to me this was severely UNDERdesigned and more like it was tossed to an intern to learn on and then nobody checked their work.
If it had been designed there would have been some thought put into what might happen if you let the program just arbitrarily open links in documents without any safety measures. That didn't happen. I thus conclude that not even a rudimentary attempt at design or change management occurred. Why waste that expense on notepad when there's AI to push?
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix oh wow, is it real? Saw it this morning and thought it was a joke.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix WTF FFS.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix how are they making the same mistakes in their products since their first email client in the 90s.
Every... Fucking... Time...
How
-
@pheonix How can you fuckup Markdown support so hard
@pheonix @NaahraTheScaled Microsoft: "Challenge accepted."
-
@pheonix oh wow, is it real? Saw it this morning and thought it was a joke.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix
I'm old enough to remember how @adamshostack re-invented application security at Microsoft and basically for most of the industry. Holy $#!+ how the times have changed
-
@pheonix vibe coder doing vibe coding things

 ️
️ -
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
-
@pheonix@hachyderm.io the thing is that there are many, many safe existing libraries to properly render and parse #Markdown without exposing yourself to RCE.
But my guess is that some project manager at #Microsoft simply went like "nah, I don't want to wrestle with those licensing issues - just implement a Markdown parser/renderer from scratch, specifically tailored for all the legacy code we have in Notepad, with this over-stretched team of 3 contractors, and get it done by the end of the quarter".
@fabio @pheonix It's not a renderer issue. It doesn't pop up a warning before opening certain URL schemes when you ctrl+click on them. Is this an issue? I don't know, conceivably but not in most Windows 11 configuration ("default" isn't really a thing). you can get a t shirt for reporting things like this if you find that interesting

-
 M mindtunes@troet.cafe shared this topic
M mindtunes@troet.cafe shared this topic