They finally did it.
-
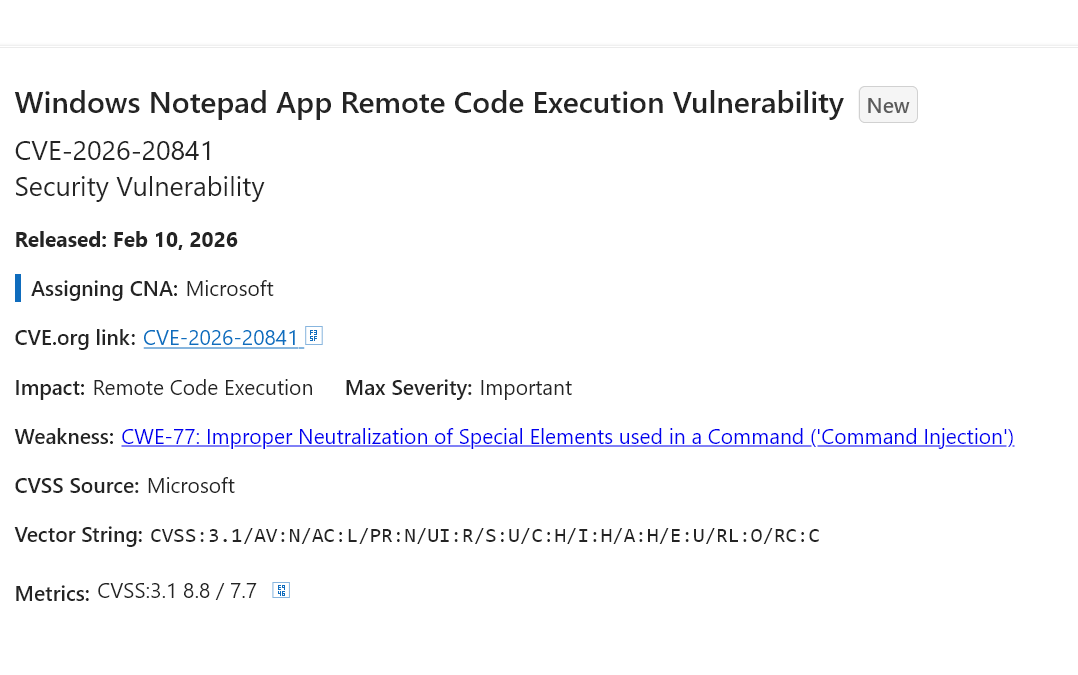
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix Windows 11 =
 ️
️ -
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix @duniamelayu Linux?
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix Don’t forget that Notepad++ was compromised recently too by state actors… https://notepad-plus-plus.org/news/hijacked-incident-info-update/
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix I believe nothing has ever been safe
 The only state that approaches it is "not compromized yet"
The only state that approaches it is "not compromized yet" 
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix Oh ffs
Right, it's back to pen and paper, so. JMJ.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
This is hilarious. Next time hire some experienced, qualified, human coders?

-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix Valt het jullie ook op dat een klaarstaande Windows-update de werking van applicaties beïnvloedt? Als programma's op een vreemde manier reageren en het icoontje "afsluiten en updaten" is zichtbaar, weet ik al weer hoe laat het is. Na updaten en herstarten werkt het dan weer normaal.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix another reason to switch on linux, only thing that can hold someone from switching is adobe software
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix @microsoft always delivers
-
@jkb @pheonix That seems to be the case, although the weakness is in Microsoft Notepad incorrectly handling “an unverified protocol”, not in something the user then has to do or interact with. Besides clicking a link.
This reads to me like an URI protocol handling issue.
And that functionality is not something they’d have to reinvent or vibe code.
You know, with their proprietary plain text editor running on their proprietary OS, and next to their proprietary file explorer, their proprietary internet browser, their proprietary email client and proprietary network agents.
All their proprietary software handling URI protocols… RIGHT THERE.
@avuko @pheonix Yes, indeed. And yes indeed this is something that should have never happened, the whole situation is shameful.
I was just pointing out that this vulnerability requires additional user input (albeit a very likely user input that normally shouldn't raise any concern), it's not one of those nightmare situations in which the mere opening of a file triggers an exploit.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix@hachyderm.io the thing is that there are many, many safe existing libraries to properly render and parse #Markdown without exposing yourself to RCE.
But my guess is that some project manager at #Microsoft simply went like "nah, I don't want to wrestle with those licensing issues - just implement a Markdown parser/renderer from scratch, specifically tailored for all the legacy code we have in Notepad, with this over-stretched team of 3 contractors, and get it done by the end of the quarter".
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
I, for one, am shocked the company going all in on spicy autocorrect keeps having worsening security issues. Thank goodness they take security seriously! /s
It is really something watching a company you hate burning itself to the ground.
-
@pheonix@hachyderm.io the thing is that there are many, many safe existing libraries to properly render and parse #Markdown without exposing yourself to RCE.
But my guess is that some project manager at #Microsoft simply went like "nah, I don't want to wrestle with those licensing issues - just implement a Markdown parser/renderer from scratch, specifically tailored for all the legacy code we have in Notepad, with this over-stretched team of 3 contractors, and get it done by the end of the quarter".
@fabio Quarter? More like a week. Just prompt some generative AI and bam, complete source code for a Markdown parser unencumbered by copyright and licensing issues, and since the AI can be prompted to be an expert in Markdown processing and secure coding which automatically ensures all generated code will be perfect in every way.
Fully ready for Microslop to ship.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix #Microsoft will never change. Security is always an afterthought.
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix Nobody who genuinely cares about infosec uses Windows unless forced by an employer.
-
@pheonix I never use Notepad for years. I prefer Notepad3 or recently I moved to Zed.
-
@pheonix Oh ffs
Right, it's back to pen and paper, so. JMJ.
@clickhere I fully concur!
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
@pheonix wait, that CVE was REAL???? I thought it was a joke
-
They finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore?

https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
I don’t understand how marked down can end up injecting AI other than a deliberate attempt to build weakness into the system. You have to work to do shit like this.